Cyber threat: in the past five years, digitalization has transformed the utility industry. But it is a shift that opens utilities to cyberattacks. GTW looks at a report by Siemens and Ponemon Institute, which assesses the vulnerabilities and preparedness of the industry.
The changing energy landscape presents utilities with opportunities. Increasing digitalization in the power sector – as a driver and facilitator of decarbonization and distributed generation – allows utilities to improve maintenance regimes or fleet performance in generating assets, for example, or bring greater transparency in transmission and distribution networks. Yet greater digitalization also means greater risk to attacks through breaches in cyber security. During the autumn of 2019, Siemens and Poneman Institute presented a report: ‘Caught in the Crosshairs: Are utilities Keeping Up with the Industrial Cyber Threat? Assessing the Operational Readiness of the Global Utilities Sector’.
It is not the first cyber security report the two organizations have produced together; others have covered oil and gas.
But recognizing that digitalization brings both clear benefits and the possibility of disproportionate risks, Siemens and the Ponemon Institute have returned to their cyber security collaboration for the new report, which assesses the state of cyber security in the utility industry.
“The report paints a picture of why you should care, what the big challenges are and what the solutions are,” said Leo Simonovich, Global Head, Industrial Cyber and Digital Security, Siemens Gas and Power.
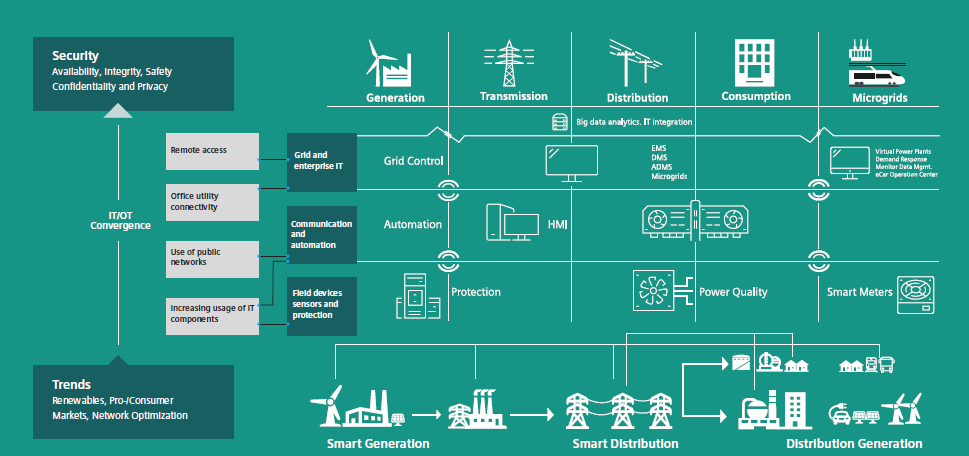
According to Simonovich, a key difference between this report and others is that it tackles the impacts of the energy transition in achieving deep decarbonization. It looks at how digitalization, the change in business models, fuel mix, and type of production, e.g. with microgrids and distributed generation are “amplifying, and in some cases helping reduce, the risk of industrial cyber attacks”.
The problem
The seriousness of cyber threats was thrust into the global spotlight in May 2017 with the Wannacry ransomware attack. It was reportedly the biggest cyber attack in history, with one security software supplier observing 57,000 infections in 99 countries across various industries.
The power sector did not escape untouched. WannaCry attacked computers at the West Bengal power distribution company in India. Officials from West Bengal State Electricity Distribution Company detected the malicious software (malware) at four of its offices.
And one of the most significant and publicly disclosed cyber security attacks on electrical transmission systems occurred in December 2015 when a cyber attack on Ukraine’s power system caused a wide area power outage that affected over 200,000 customers.
Indeed, energy is one of the top three sectors targeted for attack in the United States. According to the National Cybersecurity and Communications Integration Center, in 2016 alone the sector reported 59 incidents – 20% of the 290 total incidents reported in that year.
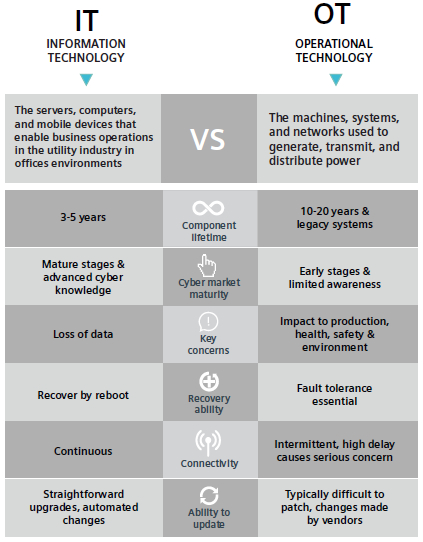
As the utility industry continues its transition from analogue to digital, from centralized power generation to a distributed system of natural gas and renewable energy, existing Operational Technologies (OT) – the machines, systems and networks used to generate, transmit and distribute power – are increasingly equipped with IT software to help operators provide the benefits of digitalization to their customers.
While the deployment of digital and networked equipment through the operating environment greatly increases the control and intelligence that organizations have over grid assets, these same technologies provide malicious attackers with new targets within a broader, more complex attack surface.
Connecting to the outside
In an effort to digitize their fleet, utilities historically viewed cyber security as an afterthought. Even when new OT assets are designed with security in mind, they are often connected to broader critical infrastructure, which lacks systemic security controls.
As utility executives incorporate distributed and digitally connected grid technologies into their asset portfolios, their ability to withstand a cyberattack is limited at best.
With regards to digitalization in the gas turbine-based power sector, Siemens points out that with digitalization “the attack surface” is being increased. Simonovich explained: “Today digitalization is happening point-to-point. Typically, you have a turbine and a control system, which have not been maintained for a number of years that is suddenly connected to the outside world – so you get to service the turbine to increase its performance, to extend its asset life, etc. But those point connections create an opening or an attack sector.
“Now there is connectivity to a world that has traditionally been air-gapped. You think you’re safe, but the problem is, because you haven’t patched, even a basic vulnerability can impact you. That’s why when you think about mega attacks like Wannacry – to deal with Wannacry all you need is a simple patch that has been around for years – the reason it adversely impacted 25% of respondents, with a high degree of potency, is because of lack of maintenance of these air-gapped environments in which turbines are operating.”
He noted that the big problem with IT solutions today is that they only look at the enterprise network. “If you look at what happened in Ukraine, Iran or Saudi Arabia, in those attacks someone was messing with the PLCs [programmable logic controllers] to spin a turbine or compressor at a different rate than intended in order to cause a safety event. But if you look at the network, the network’s fine.
“So our view of ‘visibility’ is that you have to understand what’s happening to the production process and you have to understand what’s happening in the network. And you have to bring the two worlds together – the physical and the digital worlds.
“The idea of a castle with a moat is dead as a security concept to defend against attacks because there is no such thing as a castle anymore; there are a bunch of clusters now. If you look at distributed systems, you now have clusters of production and demand response; it’s no longer castle and moat so you really need to take a defense in-depth approach to the problem.”
Even traditional centralized systems present a problem, he says, where the need for black start units for security of supply increases the cyber risk. “In a hyper-connected world, where there is a focus on creating enough redundancy, physical security and cyber security start to converge. If you look at a couple of the past attacks that have occurred at the Russian chemical facilities, all of them have had an insider threat component, but all were going after safety-critical components and back-up systems.”
How to act
According to Siemens, given the probability of a cyber breach is nearly 100%, the question for executives and security professionals becomes not whether to act, but how? Holistic cyber security emphasizes not only the need to prevent an attack but also the game plan for how to respond.
The new study surveyed a range of utility professionals responsible for securing or overseeing OT assets, i.e. everything outside the enterprise network. Research was conducted to gain a clearer picture of utilities’ existing capabilities, levels of preparedness, vulnerabilities, and strategic understanding of their OT cyber risk.
When asked what made management of OT security challenging, the most frequent response was the rise of sophisticated attacks. Because many utilities manage infrastructure critical to daily life, nation-states and other malicious actors have an interest in developing cyber weapons that target utilities. Individuals and criminal organizations may now also have the backing of nation-states, or state-aligned proxy groups, interested in damaging physical assets, and may use potent cyber warfare tools originally developed by nation-states.
For example, the powerful WannaCry or NotPetya attacks, which affected 25% of all respondents in the past two years, are public examples of attacks that harness expertise developed by nation-state actors. Unlike ransomware attacks seeking financial information, these attacks systematically destroyed information and shutdown operations. Paying ransom often does not help restore operations.
“The big challenge is not just the frequency of attacks, which have increased exponentially – the majority of respondents said they have experienced at least one attack per year in the production environment – but also the sophistication of the attacks,” said Simonovich. “Some 64% said they experienced a sophisticated attack that they were challenged to deal with. Almost all of those attacks resulted in either a shutdown, operational loss or in some cases a safety event.”
Respondents gave mixed assessments of their own organizations’ readiness to meet or respond to cyber attacks. Only 42% rated their cyber readiness as high, and only 31% were fully ready to respond to or contain a breach.
So why are utilities so challenged? The report revealed four main reasons or “blind spots”, as respondents called them. According to Siemens, the biggest of these is visibility. As Simonovich puts it, “you can’t protect what you can’t see”.
The process of digitizing equipment – replacing or adding digital controls to analogue equipment – helps utility managers increase their visibility into the operating status of assets in their fleet. Visibility also enhances cyber security capabilities by enabling operators to better understand the current status of connected assets. At its most basic level, it means knowing what is and is not connected in the OT environment, as well as how those assets behave to spot potential anomalies. Only by understanding what’s happening in their production environment can operators build the confidence to take proportionate action.
However, respondents rated their organizations’ ability to achieve comprehensive and continuous visibility of digital assets as low – with organizations in the United States and Europe reporting the lowest level of maturity among the other regions. This should concern leaders in all areas of the utility industry. It is difficult to provide meaningful security on a network when operators do not know what equipment exists within that network.
Artificial Intelligence (AI) and big data analysis are used by a minority of organizations to monitor operations and recognize threats, like an insider threat. Yet only 18% of respondents reported using big data or AI monitoring, with the practice most common in the US (23%).
While a minority of utilities use big data and AI today, these tools can help organizations overcome sleeping malware and the detection of unknown threats. Using advanced analytics, security professionals can identify anomalies in their asset behavior. With visibility and context, an analyst can trace bi-directionally activity from the OT network to the IT network; identify gaps and unpatched systems that enabled an adversary to enter a plant; and establish control and lie dormant – waiting to take over and force a shutdown.
The second blind spot was ownership. “In utilities there is always the question of who owns the OT – who owns industrial cyber,” said Simonovich. “Respondents are saying ownership is bifurcated – sometimes it’s owned by ‘operations’, sometimes it’s owned by ‘controls’.”
The report recommends having clear ownership for OT security within an organization. Assign a specific person responsibility for security and make their chain of command clear all the way to the C-suite. The rising stakes for security in the OT environment make good cyber hygiene a pressing issue for any organization in the utility sector.
The third big problem the report highlights, is the skills gap. In general, addressing cyber security requires expertise from control engineers, security specialists and network specialists, often working together. People with appropriate skills are scarce – in every region around the world, more than half of respondents indicated their organization’s staffing level was not adequate to meet cyber security objectives in the OT environment. “There are very few people out there that know networking, security, turbines etc., all in one. And there are even fewer people like that at scale,” added Simonovich.
Yet despite the human capital challenge identified in the survey, the industry overall is investing more resources into technology and compliance than into training or personnel.
The fourth big issue is having the right kind of OT solutions. “Today there are a number of IT players targeting this space,” says Siemens. “They see it as an opportunity,” said Simonovich, “but there are IT players that do more harm than good because a simple vulnerability scan can bring down a power plant.”
The report notes that these four big blind spots are magnified for small organizations, as they are particularly challenged in dealing with the problem. “Their blind spots are much more acute,” said Simonovich. “If you think about the ‘resource’ average, for example, they are lucky to have two or three people covering security, let alone OT security. So they are struggling to comply. Today, small utilities don’t know how to get scale or competence to address this problem.”
Improving preparedness
Despite the risk that a novel attack will exploit unknown gaps in security, 35% of respondents said their organization had no response plan for cyber attacks. On average, responses to past malware attacks took 72 days after an outage. Further, smaller organizations took longer (88.5 days) than larger organizations (62.6 days).
The slow response times and lack of preparation indicate major opportunities to improve preparedness. Organizations should ensure that in the event of a successful breach of security, their teams will have some ability to coordinate responses and prioritize recovery efforts.
Recognizing that each organization has unique assets, personnel, and appetite for risk, Siemens offers a few broad frameworks for building systems that continually improve security. Rather than prescribing one solution, the framework helps employees across a utility’s enterprise to evaluate and improve their cyber security systems.
As the report puts it, a sophisticated business that uses digital technologies to operate more efficiently than competitors needs to protect those technologies from attacks. Leaders within the utility industry need to allocate attention and resources to their cyber defenses commensurate with the increased risk to their businesses.
A full copy of the report can be downloaded at:
https://new.siemens.com/global/en/products/energy/services/digital-services/cybersecurity.html